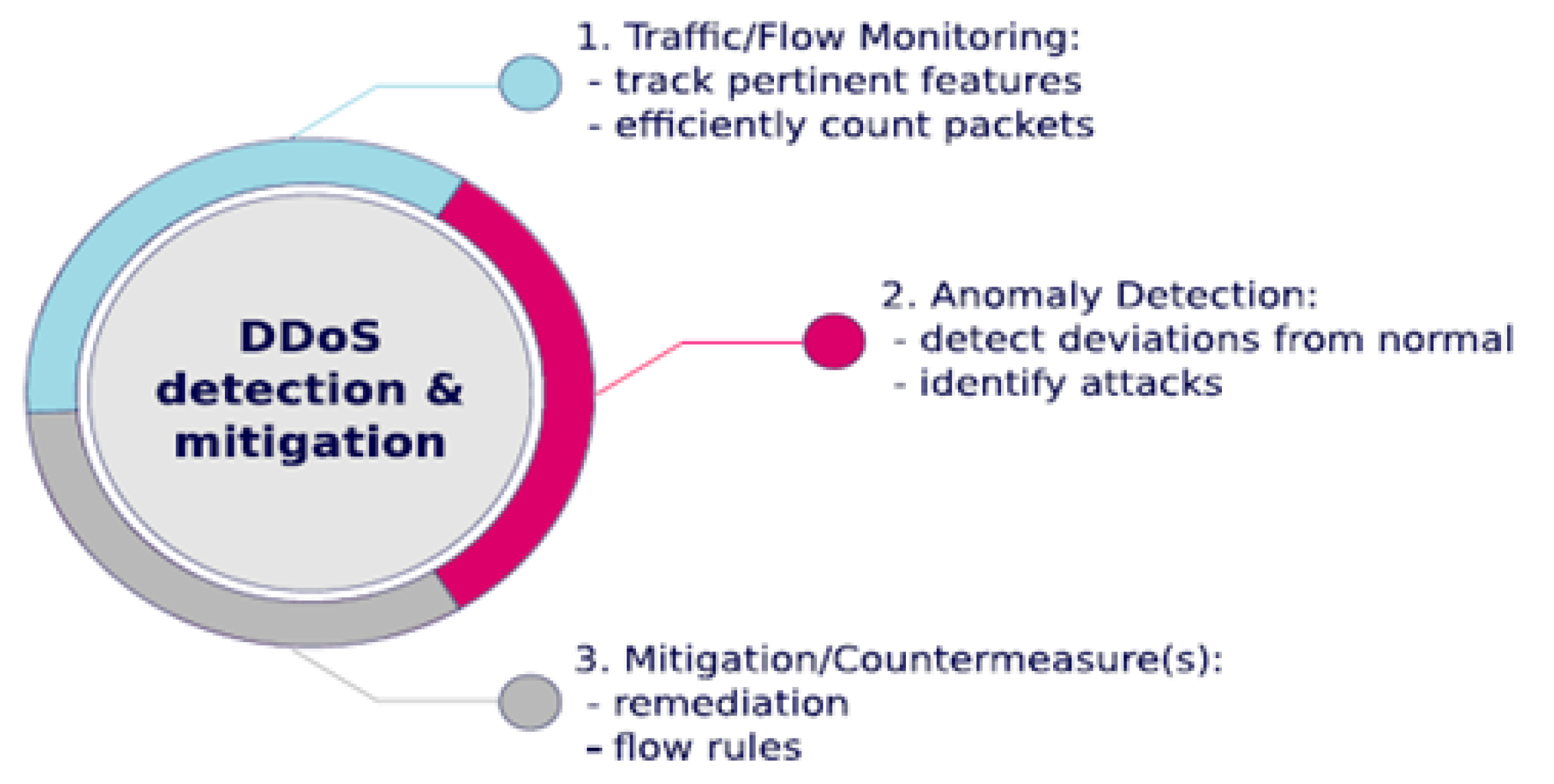
Future Internet | Free Full-Text | Effective and Efficient DDoS Attack Detection Using Deep Learning Algorithm, Multi-Layer Perceptron

How to Hack Wi-Fi: Performing a Denial of Service (DoS) Attack on a Wireless Access Point « Null Byte :: WonderHowTo
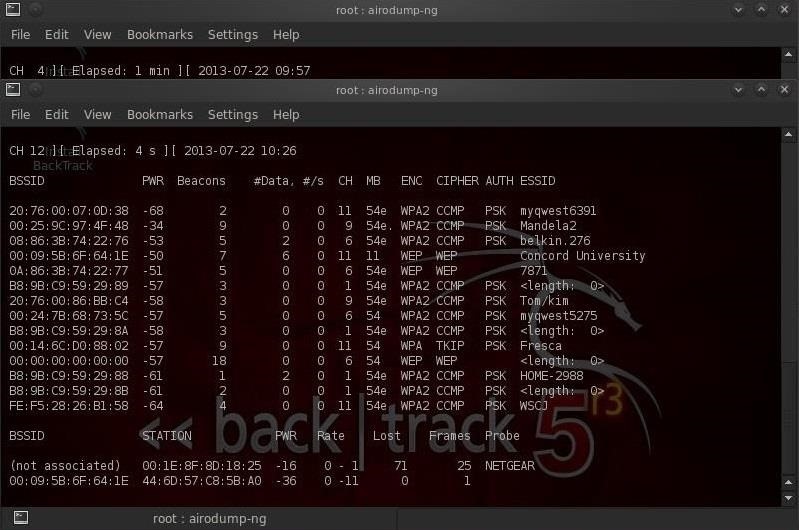
How to Hack Wi-Fi: Performing a Denial of Service (DoS) Attack on a Wireless Access Point « Null Byte :: WonderHowTo
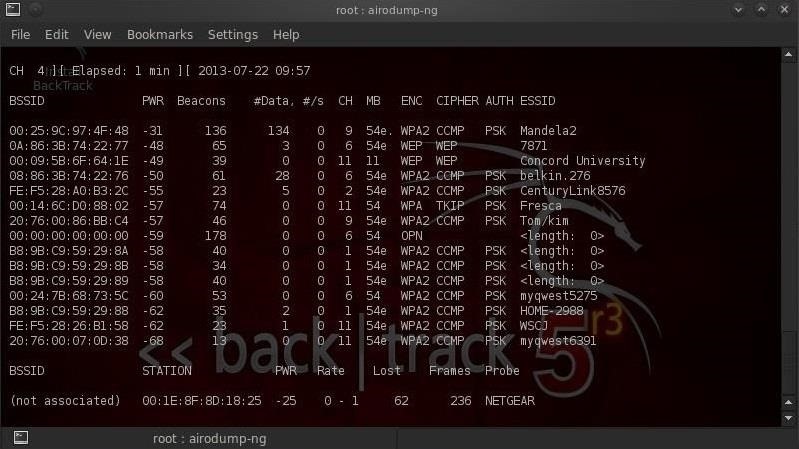
How to Hack Wi-Fi: Performing a Denial of Service (DoS) Attack on a Wireless Access Point « Null Byte :: WonderHowTo

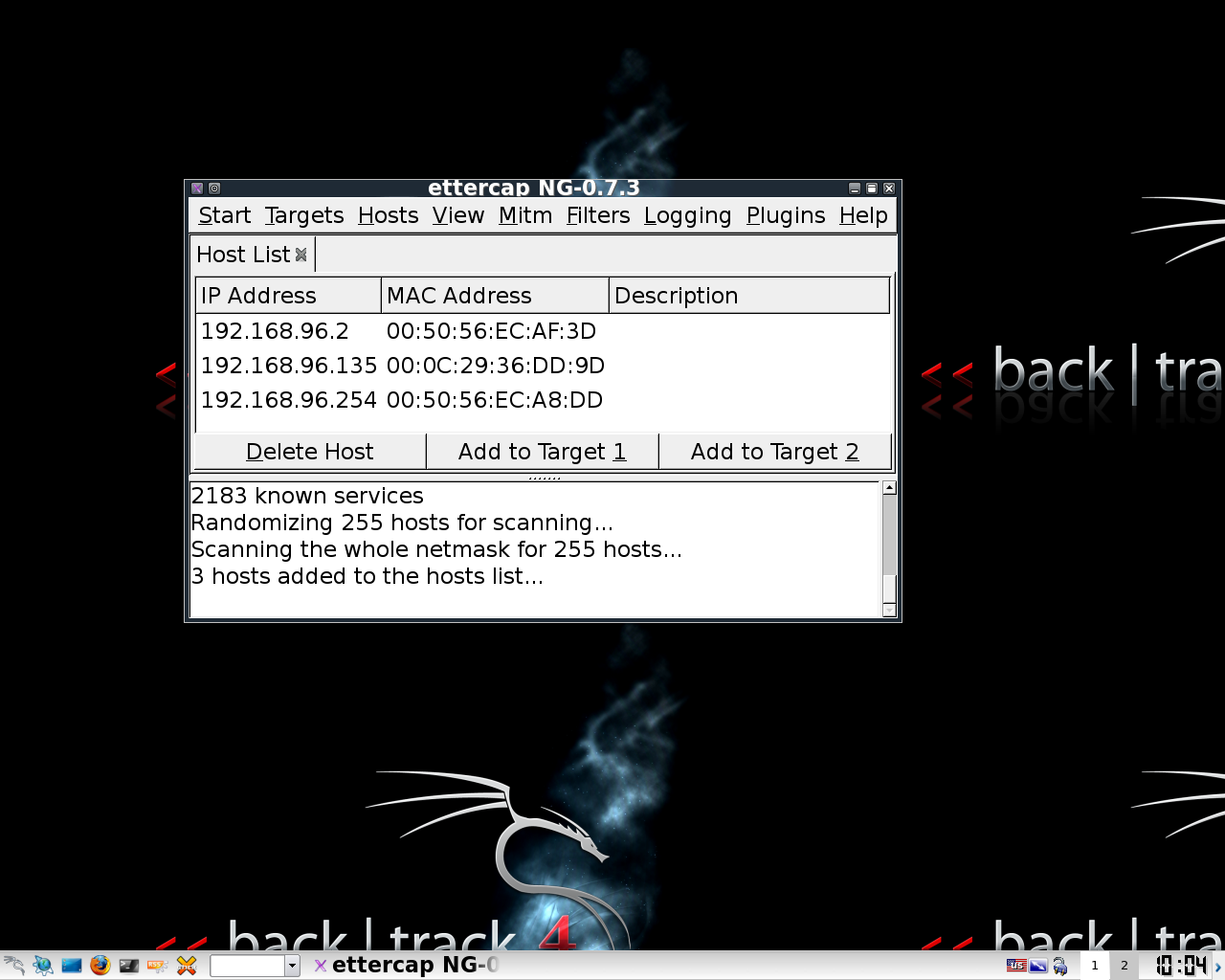
Future Internet | Free Full-Text | Effective and Efficient DDoS Attack Detection Using Deep Learning Algorithm, Multi-Layer Perceptron